
24+ Years in Business

Leader in Cryptographic Security

1,600+ Patents

24+ Years in Business

Industry Solutions
FEITIAN specializes in industry-specific security solutions designed to address the unique challenges and compliance requirements of various sectors. Our tailored solutions provide robust authentication, encryption, and access control measures to a wide range of industries. With FEITIAN’s industry-specific solutions, organizations can strengthen their cybersecurity posture, protect sensitive data, and meet standards and regulations with confidence.
Find Your Industry Solution

Healthcare: FEITIAN offers industry-specific security solutions to safeguard sensitive data, protect medical systems from unauthorized access, and ensure compliance with healthcare regulations such as HIPAA, HITRUST, and EPCS.

Finance: FEITIAN provides comprehensive security solutions for the financial sector, including secure authentication and transaction verification, protection of customer data, fraud prevention, and regulatory requirements.

Government: FEITIAN offers government-grade security solutions tailored to meet the unique needs of federal, state and local government agencies and departments. Products that support PIV standards for employee converged access, as well as information security standards like FIPS 120 and FIPS 140-2 are currently in use. FEITIAN’s federal portfolio includes products that are TAA compliant to meet supply chain procurement requirements.

Enterprise: FEITIAN delivers enterprise-grade security solutions that address the complex security challenges faced by large organizations across various industries. These solutions include multi-factor authentication, secure access controls, identity and access management, and encryption technologies, empowering enterprises to protect their valuable assets, sensitive data, and intellectual property from cyber threats and unauthorized access.
featured solutions
Enterprise Security Solutions
Includes multi-factor authentication, secure access controls, identity and access management, and encryption technologies, ensuring robust protection against cyber threats and unauthorized access.
Government Security Solutions
Includes smart card and PIV solutions, FIDO authentication, secure key management, and encryption technologies, empowering safeguarding critical infrastructure, securing sensitive data, and ensuring compliance with stringent requirements such as FIPS 201 and FIPS 140-2.
Education Security Solutions
Includes multi-factor authentication, secure physical and logical control, identity management, and secure key storage, enabling educational institutions to protect student and staff data, secure campus resources, and ensure a safe learning environment.
Healthcare Solutions
Includes strong authentication, secure logical and physical access control, and encrypted communication to protect access to patient data, safeguard medical systems, and ensure compliance with data privacy regulations.
Financial Insitution Security Solutions
SMB & Personal Security Solutions
Critical Infrastructure Security Solutions
Includes hardware tokens, smart cards, and biometric devices, providing secure and reliable authentication methods to protect critical systems, data, and infrastructure assets. These solutions help safeguard against unauthorized access, mitigate cyber threats, and ensure the integrity and availability of critical infrastructure operations.
Case Studies & White Papers

Authentication, White Paper
Best Practices for Seamless FIDO Implementation
A complete overview of the FIDO authentication framework, its key principles, and the benefits it offers for enhancing security and user experience.

Authentication, Solution Note
Healthcare institutions are held to high standards in the U.S. through HIPPA, HITRUST, and FIPS for securing systems, data, transactions, communication, access, authentication, and more.

Authentication, Company News
Introducing FKaaS: FEITIAN Keys as a Service
With FKaaS, enterprises can now access FEITIAN's FIDO Certified phishing-resistant multi-factor authentication (MFA) security in a more flexible and scalable manner.

Authentication, Solution Note
Duo + FEITIAN = Phishing Resistant FIDO2 MFA
Cisco Duo helps companies protect their data at scale with zero trust security platform – pair it with FIDO Certified keys from FEITIAN for phishing-resistant MFA.

Authentication, Solution Note
Revolutionizing Banking Security with FIDO
Passwords, OTPs, and 2FA are no longer enough to negate cyber criminals, especially for sensitive environments like banking and finance institutions.
Authentication, Case Study
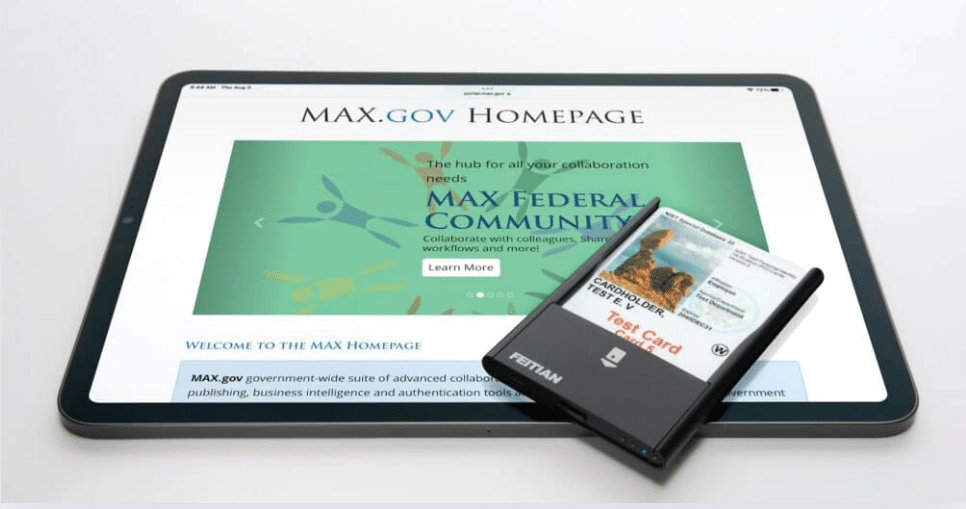
Empowering Government Agencies With PIV & CAC Sign-
A groundbreaking solution developed by our longstanding technology partner, Twocanoes, offers a game-changing approach to PIV and CAC card authentication on iOS devices.
Authentication, Solution Note
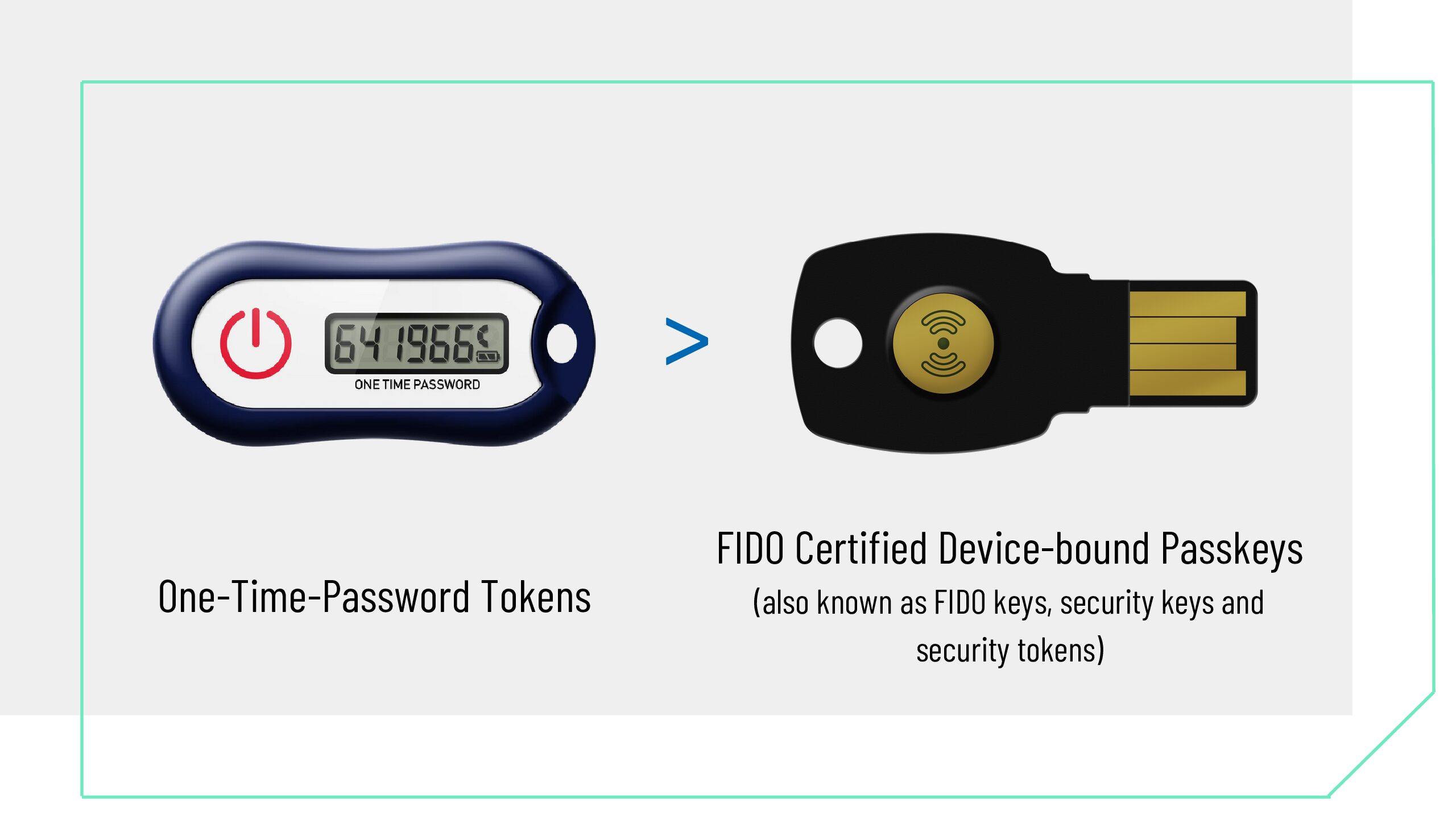
OTP to FIDO Transition Solution Note
Download our Solution Note to discover how FEITIAN can help upgrade your authentication security from legacy OTP, to FIDO security Keys.
Authentication, Case Study
Case Study: Enterprise
This case study profiles one of our longstanding enterprise customers who selected and deployed FEITIAN FIDO2 security keys as part of their passwordless journey.
Authentication, Solution Note
Microsoft Entra ID Solution Note
Download our solution note to discover how FEITIAN and Microsoft Entra ID can safeguard your digital assets today.

Authentication, Solution Note
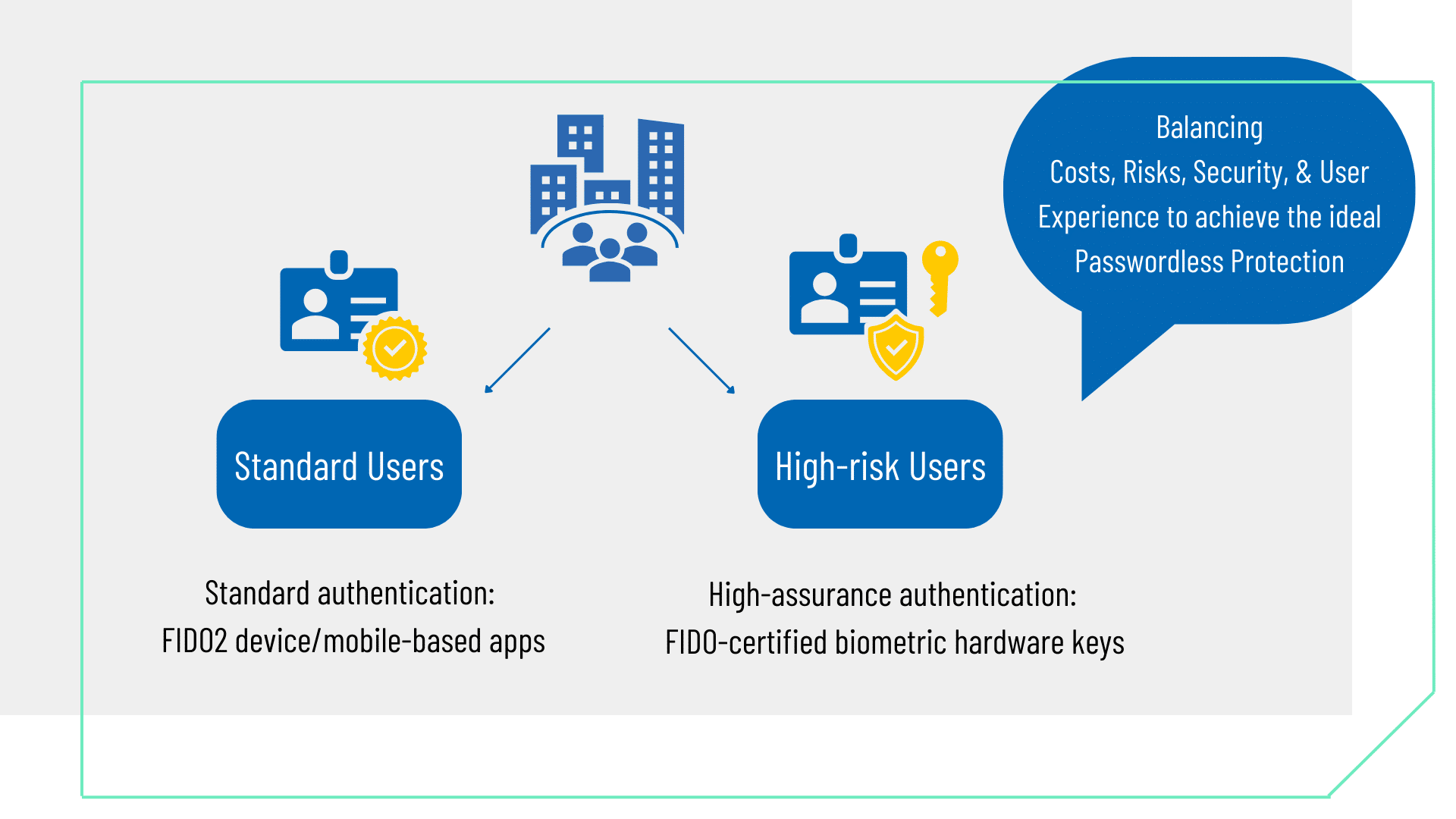
FIPS + FIDO Solution Note
True Passwordless Protection from FEITIAN with FIPS + FIDO Certified Keys.

Authentication, White Paper
Everything You Need to Know About Fido
A comprehensive overview of the FIDO (Fast Identity Online) authentication framework, it's key principles, implementation, and the benefits it offers for enhancing security and user experience.
Authentication, Solution Note
What Role Does Multi-Factor Authentication Play in Cyber Security
In today's digital age, cyber threats are on the rise, and it is more important than ever to secure every endpoint and data. With the increasing frequency and sophistication of cyber-attacks, traditional authentication methods like usernames and passwords are no longer enough.
Authentication, Solution Note
Different Types of MFA & What You Need to Know
Multi-factor authentication (MFA) is a vital component of digital security, neutralizing the risks associated with compromised passwords. Different types of MFA, such as phone callbacks, SMS-based OTP, OTP tokens, and mobile authenticator apps, offer varying levels of security and convenience.
Coming Soon…
Looking for a specific resource? Let us know!
SIGN UP TO DOWNLOAD
Already submitted? Check your email for the download link.
Certifications




Relevant Posts

3 Ways to Meet Upcoming CJIS Authentication Mandates

Outsmarting Attackers by Deploying FIDO2 in Education

FEITIAN’s Secure your Summer FIDO Sale
Questions? Get In Touch With Our Support Team
We understand the importance of timely and reliable support when it comes to your security solutions. By filling out our contact support form, you can reach out to our experts who will provide prompt and personalized assistance to address your specific needs


