Cyber Security for Government
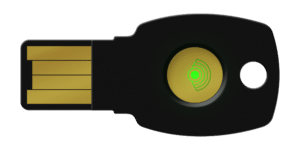
Protecting sensitive data, critical infrastructure, and national security is of paramount importance. FEITIAN offers comprehensive cybersecurity solutions specifically designed for government agencies, providing robust authentication solutions, secure access control, multi-factor authentication, and encryption technologies.
With FEITIAN’s expertise and advanced solutions, government organizations can enhance their cyber defenses, detect and respond to threats in real-time, and uphold the trust and security of their citizens’ data and vital systems.
FIPS 140-2 sets stringent standards for cryptographic modules utilized in safeguarding sensitive government information. Compliance with FIPS 140-2 signifies adherence to rigorous criteria regarding encryption strength, secure design, and resistance to various forms of exploitation. Government agencies worldwide rely on FIPS 140-2 certification to ensure the integrity, confidentiality, and availability of their data.

Government Authentication Use Cases
Authentication for Government Portals
Secure Remote Access
Access to Restricted Areas
Cyber Risks in Government
Nation-state attacks
Insider threats
Cybercriminal activities
Suggested products
Government Cyber Security Benefits

Enhanced security

Streamlined access control

Scalability and flexibility

Regulatory compliance

User convenience

Cost-effectiveness
Relevant Posts

Unlock the Future: FEITIAN Products and Google’s New Passkey Feature
FEITIAN MFA Cryptographic Module has achieved the FIPS 140-2 level 2
Use FEITIAN FIDO security key to protect your Apple ID
Questions? Contact Sales
We understand that finding the right security solutions for your business is crucial, and our dedicated sales team is here to assist you every step of the way. By filling out our sales support form, you can connect with our knowledgeable sales representatives who will guide you through the process, answer your questions, and provide tailored recommendations based on your unique requirements.
Contact information:
408-352-5553
2580 N First St. Suite 130, San Jose, CA 95131
sales@ftsafe.us
"*" indicates required fields